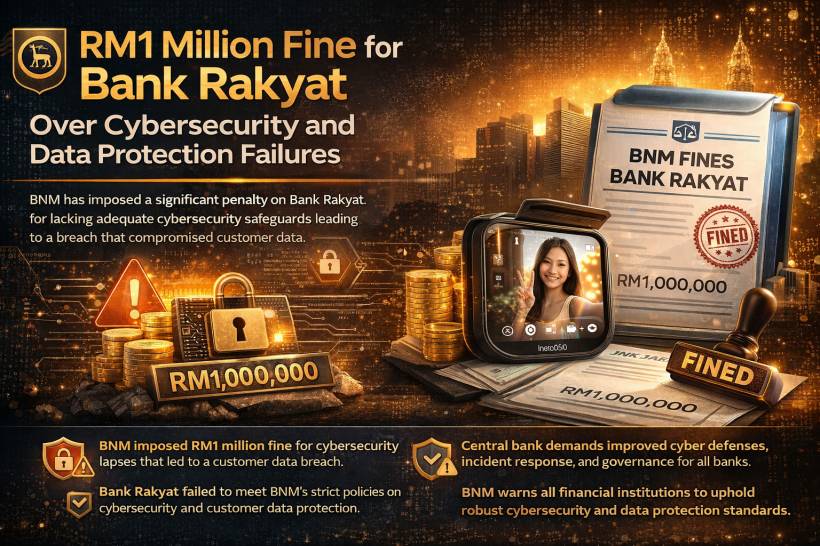
Cybersecurity failures in the banking sector are never a small matter, and this latest action by Bank Negara Malaysia sends a very clear message. Bank Kerjasama Rakyat Malaysia Bhd, better known as Bank Rakyat, has been fined RM1 million after the central bank found weaknesses in its cybersecurity controls and incident response that contributed to a breach involving customer data.
The penalty highlights how seriously regulators are treating cyber resilience today, especially in industries that handle sensitive financial and personal information. For banks, having digital services is no longer enough. They are also expected to prove that their systems, processes, and response capabilities are strong enough to withstand modern cyber threats.
Why Bank Negara Malaysia Took Action
According to Bank Negara Malaysia, the issue stemmed from a cyberattack that resulted in unauthorised access to Bank Rakyat's information technology systems. Following its review, the central bank concluded that the bank had failed to meet important requirements related to cybersecurity and customer data protection.
The RM1 million fine was imposed on January 20, and Bank Rakyat settled the penalty on January 26, 2026. Bank Negara also noted that the bank has since taken remedial steps to strengthen its cybersecurity posture, including improvements to its ICT controls, governance arrangements, and resource management.
That part is important, because regulatory action is not only about punishment. It is also about forcing corrective action so the institution can reduce the risk of the same type of incident happening again.
The Bigger Issue Behind the Fine
This case is not just about one bank being fined. It also reflects a broader reality in financial services. Cybersecurity today is closely tied to public trust.
Customers expect banks to protect not only their money, but also their personal and transactional information. Once that trust is shaken, the impact can go beyond regulatory penalties. It can affect reputation, customer confidence, and even how quickly an institution can recover from an incident.
In many cyber incidents, the real problem is not just that attackers got in. The bigger concern is often whether the organisation had enough safeguards in place beforehand, and whether it responded quickly and effectively once something went wrong. That is why regulators pay close attention not only to preventive controls, but also to response plans, recovery processes, and internal governance.
The Two Key Policy Areas Involved
Bank Negara Malaysia pointed to two major policy requirements that financial institutions are expected to follow.
The first is the Risk Management in Technology policy document. This requires banks to maintain strong cybersecurity practices that can detect, prevent, and respond to threats. It also expects financial institutions to have clear plans for incident handling, service recovery, and communication during and after a cyber event.
The second is the Management of Customer Information Permitted Disclosures policy document. This focuses on protecting customer data through proper safeguards that reduce the risk of theft, misuse, or unauthorised access. It also places emphasis on active system monitoring so suspicious activity can be identified early.
Taken together, these requirements show that cybersecurity is not treated as a narrow IT issue. It is a governance, compliance, and operational responsibility that must be managed across the organisation.
A Warning to the Financial Industry
Bank Negara's statement also carried a broader warning. The regulator made it clear that strict action will be taken against financial institutions that fail to comply with legal and regulatory expectations.
That should not come as a surprise. Banks sit at the centre of the financial system, and any weakness in security can have consequences far beyond a single organisation. As attacks become more sophisticated, regulators are under increasing pressure to ensure that banks do not treat cybersecurity as an afterthought.
This also means financial institutions can no longer rely on basic controls or outdated response processes. They need continuous monitoring, better preparedness, stronger governance, and enough skilled resources to manage evolving threats properly.
Why This Matters to Customers
For ordinary customers, this development is a reminder that cybersecurity incidents are not always visible at first. A bank may continue operating normally on the surface, but behind the scenes, weaknesses in systems or response processes can still create serious risks.
Regulatory enforcement helps hold institutions accountable, but customers also benefit when such cases push banks to improve security standards across the board. Stronger controls, faster detection, and better incident response all reduce the chances of data exposure and service disruption in the future.
Final Thoughts
The RM1 million fine on Bank Rakyat is more than just a penalty headline. It reflects a growing expectation that banks must take cybersecurity, incident response, and customer data protection seriously at every level.
For financial institutions, the lesson is straightforward. Cybersecurity is no longer just about deploying tools or meeting minimum technical requirements. It is about building a mature, well-governed security framework that can prevent incidents, respond effectively when attacks happen, and protect customer trust at all times.
And for the wider banking industry in Malaysia, this case is a clear signal that regulators are watching closely and are prepared to act when standards fall short.




Comments