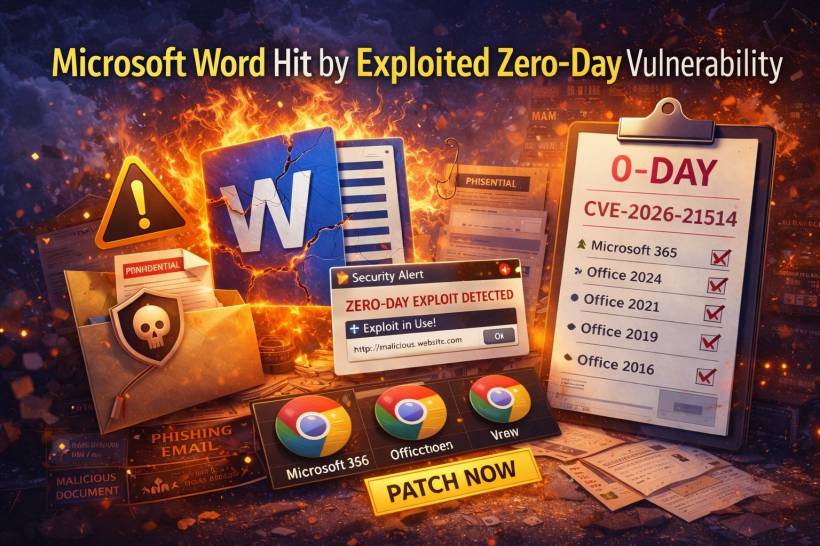
If your day involves opening Word files from emails, shared drives, or chat apps, this is the kind of security warning that shouldn't sit around waiting for "when we have time." Security teams are tracking a new Microsoft Word zero-day that's already being exploited in real-world attacks. What makes it especially worrying is that it's not the classic "macro prompt" situation. This flaw can be used in a way that bypasses some of the protections and warning flows users normally rely on before a document does something risky.
LEMON BLOG
If you use Google Chrome on desktop, this is one of those security stories where the boring advice is also the correct advice: update immediately. Google has released urgent security updates for a zero-day vulnerability that's already being actively exploited in the wild. In other words, attackers aren't waiting for you to patch, they're counting on you not doing it
Microsoft has recently confirmed a critical zero-day vulnerability affecting the Windows Remote Access Connection Manager (RasMan) service. The flaw, tracked as CVE-2025-59230, poses a serious risk to enterprise systems, enabling attackers to escalate privileges from low-level user accounts to full SYSTEM-level access. Security researchers have verified that this exploit is already being actively used in the wild, prompting urgent calls for immediate patching.
A newly disclosed zero-day vulnerability in Windows shortcut files (.lnk) has been exploited in-the-wild for several years by state-sponsored hacking groups. Identified as ZDI-CAN-25373, the flaw allows attackers to silently execute malicious commands using shortcut files—making it difficult to detect through traditional security tools.
Security researchers revealed that this vulnerability has been abused since at least 2017 by advanced persistent threat (APT) groups linked to 11 different countries.
LEMON VIDEO CHANNELS
Step into a world where web design & development, gaming & retro gaming, and guitar covers & shredding collide! Whether you're looking for expert web development insights, nostalgic arcade action, or electrifying guitar solos, this is the place for you. Now also featuring content on TikTok, we’re bringing creativity, music, and tech straight to your screen. Subscribe and join the ride—because the future is bold, fun, and full of possibilities!