If you are using an iPhone in Malaysia and have been putting off software updates, this is one of those moments where delaying really is not worth the risk. Security researchers from Google Threat Intelligence Group, iVerify, and Lookout have uncovered a newly documented iPhone exploit chain called DarkSword, and Malaysia is among the countries where related activity has been observed. The attack is especially concerning because it is not the kind of old-school malware people imagine downloading by mistake. In many cases, simply landing on a compromised website can be enough to trigger the attack.
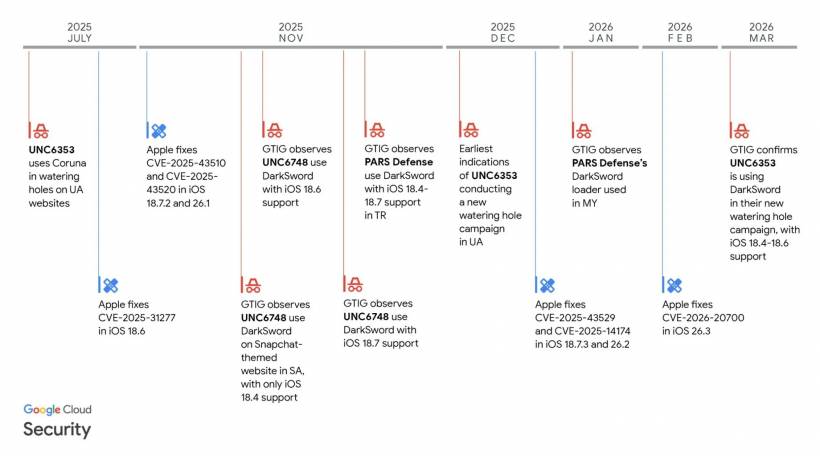
What makes this more unsettling is that DarkSword is not being described as a narrow, isolated incident. Researchers say it has been used in multiple campaigns by different threat actors, including commercial surveillance operators, and some of those campaigns were tied to activity affecting users in Malaysia and Turkey. That means this is not just a faraway cyber-espionage story happening somewhere else. Malaysia is already part of the conversation.
This Is Not Just "Another iPhone Bug"
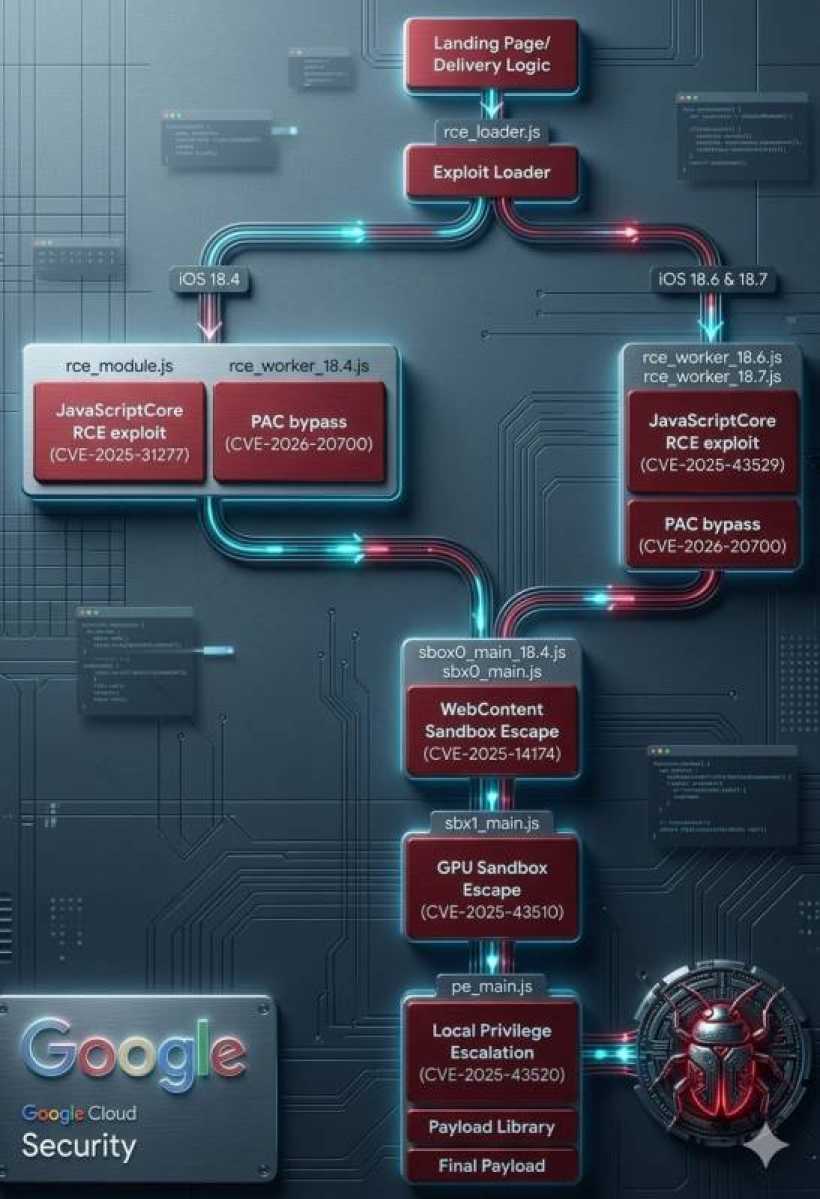
It is easy to look at security news and assume it is all technical noise. But DarkSword stands out because of how complete the attack chain appears to be. According to the researchers, it targets iPhones running vulnerable iOS 18 builds, particularly versions in the iOS 18.4 to 18.6.2 range, and it uses a chain of six vulnerabilities to gain deep control over the device. Once successful, it can access highly sensitive information such as messages, passwords, iCloud-related data, browsing material, and even cryptocurrency wallet information.
This is why the story matters beyond cybersecurity circles. For most people, an iPhone is no longer just a phone. It is banking access, work communication, family chats, personal photos, cloud storage, authentication codes, and sometimes even business records. When an exploit like this reaches that level of access, it stops being an abstract technical threat and becomes a very personal one.
How DarkSword Works in the Real World
One of the more worrying parts of DarkSword is how quietly it operates. Researchers describe it as a fileless attack. In plain language, that means it does not need to leave behind the kind of obvious spyware footprint many people associate with infected devices. Instead, it hijacks legitimate processes on the phone, steals what it wants, and then disappears. The dwell time can be just minutes, which makes detection much harder.
The delivery method is also familiar to security teams but still dangerous for everyday users: watering hole attacks. Rather than targeting victims one by one through direct messages or suspicious app downloads, attackers compromise websites that their intended victims are likely to visit. A malicious iframe on one of those sites can be enough to kick off the exploit chain. That is part of what makes this style of attack so effective. The victim may feel they did nothing risky at all, because from their point of view they were just browsing the web.
Why Malaysia Should Pay Attention
When cyber threats make global headlines, Malaysia is often mentioned only in passing, if at all. This time, that is not the case. Researchers specifically said activity linked to DarkSword campaigns was observed in Malaysia, and Google's reporting connected the Malaysia and Turkey campaigns to the Turkish commercial surveillance vendor PARS Defense. That does not automatically mean every Malaysian iPhone user is being directly hunted, but it does confirm that the local threat surface is real.
That is important because many users in Malaysia still assume iPhones are effectively immune to serious compromise. Apple devices do have strong security protections, but no platform is untouchable. What DarkSword shows is that attackers are willing to spend heavily to break into iPhones, and once those exploit chains exist, they may spread beyond elite state operations into a wider commercial or secondhand market. Google, Lookout, and iVerify all point to signs that multiple groups have been using this exploit kit rather than a single isolated operator.
The Bigger Problem Behind the Headlines
There is a larger story here too. DarkSword was reportedly discovered during investigations into another exploit kit called Coruna, and both were found on related infrastructure. Researchers have raised the possibility that powerful iPhone exploit chains are no longer remaining in the hands of a tiny number of elite actors. Instead, they may be entering a broader market where commercial surveillance vendors and other groups can reuse or repurpose them.
That shift matters. It suggests we may be moving into a phase where advanced iPhone exploitation is becoming more accessible, more reusable, and potentially more common. For ordinary users, the technical details are less important than the practical reality: attacks that once sounded too sophisticated to worry about are becoming more industrialised.
Another troubling detail is that researchers found DarkSword code left online with explanatory comments. That kind of operational sloppiness is unusual for top-tier covert operations, and it raises concerns that the tool could be studied, modified, or copied more easily by others.
Who Is Most at Risk?
Not every iPhone owner faces the same level of danger. These kinds of exploit chains are often used against people of special interest, such as journalists, activists, executives, political targets, government-linked individuals, or those operating in sensitive industries. But that does not mean everyone else can ignore the story. Watering hole attacks widen the net by compromising websites that broader groups may visit, and financially motivated criminals may also see value in a tool that can grab credentials, cloud access, and crypto wallet data quickly. Reuters reported that researchers see possible criminal uses alongside surveillance activity.
So while the highest-risk victims may still be more targeted than average users, the safer mindset is not "this won't happen to me." It is "my phone contains enough valuable data that I should not take chances."
The Good News: There Is a Clear First Step
The most immediate protection is straightforward: update your iPhone. Researchers say Apple has already addressed the vulnerabilities used in the attack chain, and iVerify recommends moving to iOS 18.7.6 or iOS 26.3.1 to mitigate them. Apple has also blocked identified malicious domains in Safari Safe Browsing, which helps reduce follow-on exploitation from known infrastructure.
For users with older devices that cannot move to the newest software, the situation is less comfortable. They may remain more exposed while waiting for any additional legacy patches. In those cases, Lockdown Mode becomes worth considering, especially for anyone who works in a sensitive role or feels they may be at elevated risk. Reports also note that the exploit was ineffective on Apple's newer iPhone 17 models when Memory Integrity Enforcement was enabled.
Why This Still Matters Even If You Think You Already Updated
One reason stories like this keep resurfacing is simple: many people do not update quickly. Apple's latest developer-facing usage figures, based on App Store activity measured on February 12, 2026, show that 66% of all iPhones were on iOS 26, while 24% were still on iOS 18 and 10% were on earlier versions. That does not tell us exactly how many remain on the specific vulnerable builds, but it does show there is still a very large pool of devices not yet on the latest major platform.
That gap between available patches and real-world user behaviour is where attackers thrive. A security update only helps after it is installed. Until then, even a very well-designed device can still be exposed.
What Malaysian iPhone Users Should Do Right Now
The practical advice here is not dramatic, but it matters. Update to the latest supported iOS version as soon as possible. Be careful with unfamiliar links and obscure websites, especially if they are sent through messages or appear through unexpected redirects. Consider Lockdown Mode if you are in a higher-risk profession or role. And do not assume that using an iPhone automatically places you outside the reach of serious cyber threats.
DarkSword is not just a story about a clever exploit chain. It is a reminder that mobile security is now tightly tied to everyday life. In Malaysia, where smartphones sit at the center of banking, work, communication, and identity, staying updated is no longer just a good habit. It is basic digital self-defense.
Final Thoughts
The biggest lesson from DarkSword is not that iPhones are suddenly unsafe. It is that modern cyber threats are becoming faster, quieter, and more commercialised. Malaysia being named in these campaigns makes the issue feel much closer to home, and rightly so. For most users, the smartest response is also the simplest one: stop postponing updates, keep your device current, and treat mobile security as something real, not theoretical.





Comments