Active Directory is one of those things that "just works" in most Windows environments, which is exactly why attackers love it. When something in the authentication chain can be bent the wrong way, the blast radius isn't a single machine. It's the entire domain.
That's the concern behind CVE-2025-33073: a Windows SMB client authentication vulnerability tied to NTLM reflection that can be used to escalate privileges and, in the worst case, end in complete Active Directory compromise.
What's Actually Going Wrong Here
At a high level, the issue sits in how Windows handles certain NTLM authentication flows. In normal operation, NTLM uses a challenge-response process. But in this case, attackers can abuse reflection and relay behavior to make a privileged Windows process authenticate "in the wrong direction" and then reuse that authentication to gain higher privileges.
Researchers categorize it as an improper access control problem, because the system ends up allowing actions that should not be allowed based on the original authentication intent.
Why This One Is Dangerous in Real Environments
The scary part isn't just that it exists. It's that research published months after the fix suggests many enterprise networks still haven't adopted the patch broadly.
In practical terms, testers report seeing vulnerable hosts frequently across:
So even if an organization thinks, "We patched our important servers," gaps in the wider environment can still be enough for an attacker to get traction.
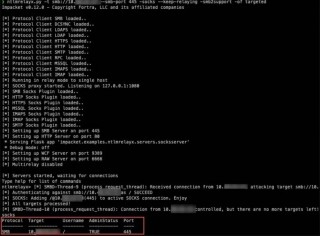
The Core Trick: Forcing SYSTEM to Authenticate Outward
A lot of modern Windows domain attacks are built around the same nasty idea: don't break crypto, just force a trusted machine to authenticate to you.
In this case, coercion techniques (such as PetitPotam, DFSCoerce, and Printerbug) can be used to push lsass.exe (which often runs as SYSTEM) into authenticating to attacker-controlled infrastructure.
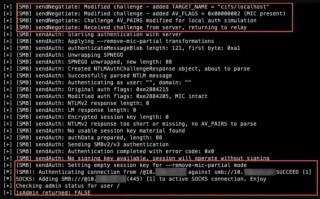
Under the hood, when a client processes an NTLM_CHALLENGE that is marked for local authentication, Windows creates a context object and places a context ID into a specific field (the Reserved field). That mechanism can be manipulated as part of the reflection/relay chain, leading to the attacker effectively gaining a privileged authentication token they shouldn't have.
Once the attacker-controlled server has a usable privileged authentication context, the next step is to leverage it to perform actions as SYSTEM, which can quickly escalate to domain-level impact.
What Attackers Need First (And Why It's Often Easy)
This isn't necessarily an "anyone on the internet" issue. The typical setup requires an attacker to be able to control name resolution or influence where a machine connects. The common paths discussed are:
The problem is that in many environments, Authenticated Users can create DNS records by default in Active Directory-integrated DNS zones. If that hasn't been tightened, a relatively low-privileged account can set the stage for something much bigger.
"We Have SMB Signing" Isn't Always the End of the Story
A lot of defenders hear "NTLM relay" and respond with "We enforce SMB signing." That's normally a strong mitigation. But research around this vulnerability highlights a more complicated reality: attackers may still succeed using cross-protocol relays, including relaying from SMB to LDAPS, even when signing and channel binding are in place.
One technique described involves manipulating NTLM negotiation behavior by stripping certain NTLMSSP flags related to signing/sealing while keeping integrity properties intact (such as the Message Integrity Code). The practical takeaway is simple: relying on a single control can be risky when attackers can pivot across protocols.
Bigger Than SMB: Where This Can Go Next
One of the reasons this vulnerability gets so much attention is that the exploitation paths don't have to stop at SMB-to-SMB relays. Researchers report successful cross-protocol targeting of services such as:
And once an attacker can operate with SYSTEM-level authority in the right place, the conversation quickly turns into domain takeover tactics, including changes to group memberships and directory replication abuse (the kind of access that enables credential harvesting at scale).
The Patch Was Released, But the Window Stays Open If You Don't Deploy It
Microsoft released fixes for this in the June 2025 Windows security updates, but the recurring theme in follow-up research is that adoption has lagged. In security terms, that creates a long-lived opportunity: attackers don't need a brand-new zero-day if last year's fix is still missing in enough places.
What Security Teams Should Prioritize
If you're looking at practical defense moves, the order of operations is straightforward:
Apply the June 2025 Windows security updates broadly, not just on "important servers." Attack chains often start on workstations.
Enforce signing and channel binding where applicable, but also assume attackers may pivot across protocols. Audit authentication paths rather than focusing only on SMB.
Review the ACLs on AD-integrated DNS zones. If Authenticated Users can create arbitrary records, you're giving attackers an easy setup step.
Look for systems and services that can be coerced into authenticating outward, and validate whether relay paths exist to sensitive targets (LDAPS, AD CS, management endpoints, database services).
The Bottom Line
CVE-2025-33073 is a good example of a modern Windows enterprise risk: not a single dramatic exploit moment, but a chainable weakness that becomes catastrophic when combined with coercion, relay techniques, and common default configurations.
If an attacker can get even modest access inside a network, this kind of flaw can provide a path from "one foothold" to "own the domain." The fix exists. The urgent part is making sure it's actually deployed everywhere it needs to be.







Comments