Cybercriminals have found a new way to break through two-factor authentication (2FA), a security feature once thought to be one of the most effective defenses against unauthorized access. Using a sophisticated phishing kit called Astaroth, hackers can now intercept login credentials and authentication codes in real time, putting accounts at serious risk.
LEMON BLOG
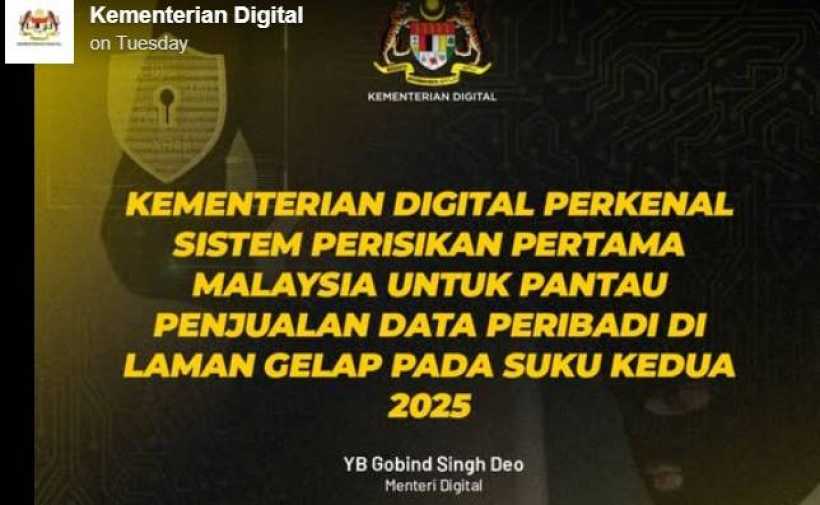
In an effort to clamp down on personal data leaks, Malaysia's Digital Ministry is rolling out its first-ever intelligence system to track and monitor the online sale of personal data. Dubbed the "Threat Intelligence Capacity Support Automation for Personal Data Breach Case Management Project", the initiative—led by the Personal Data Protection (PDP) Commissioner—is set to launch in Q2 this year. (Yes, the name is a mouthful, but at least it sounds impressive enough to scare off data thieves.)
Because if scammers love wasting people's time, why not return the favor?
In a world where scammers lurk behind every random WhatsApp message claiming you've won a mysterious lottery or inherited money from a long-lost prince, one Singaporean genius, Dylan Tan, decided enough was enough. Instead of just blocking and reporting these scammers, he built an AI to waste their time. Meet SOHAI: Scammers On Hold AI.
And yes, we know what SOHAI sounds like in Singlish. That's the point.
The modern workplace has experienced a profound shift in recent years, with hybrid work becoming standard practice and businesses rapidly embracing cloud-based Software-as-a-Service (SaaS) applications to support this new paradigm. Applications like Microsoft 365 and Google Workspace now serve as the cornerstone of business operations, driving seamless collaboration and productivity. However, this growing reliance on SaaS solutions has also attracted an increase in cyberthreats, putting critical business data at risk from attacks like ransomware and phishing.
LEMON VIDEO CHANNELS
Step into a world where web design & development, gaming & retro gaming, and guitar covers & shredding collide! Whether you're looking for expert web development insights, nostalgic arcade action, or electrifying guitar solos, this is the place for you. Now also featuring content on TikTok, we’re bringing creativity, music, and tech straight to your screen. Subscribe and join the ride—because the future is bold, fun, and full of possibilities!