If you use Google Chrome on Windows, macOS, or Linux, this is one of those updates you don't want to "get around to later." A security advisory from Akati Sekurity highlights two high-severity Chrome vulnerabilities that could expose users to arbitrary code execution (ACE) and denial-of-service (DoS) attacks.
The key theme here is simple: the bugs live in places attackers love (the JavaScript engine and media processing), and exploitation can be triggered just by visiting a specially crafted site.
What was found and why it matters
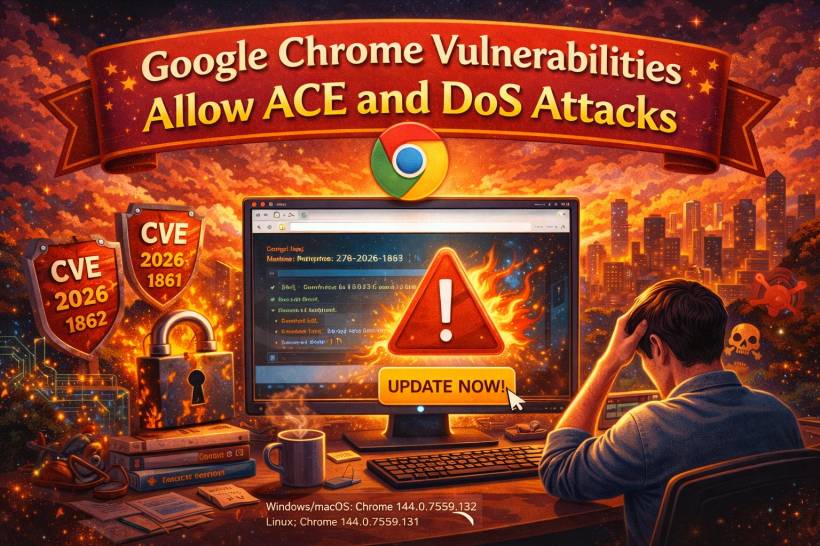
The advisory flags two CVEs: CVE-2026-1862 and CVE-2026-1861, both rated 8.8 (CVSS 3.1).
They're described as type confusion and heap buffer overflow issues — the kind of memory-corruption vulnerabilities that can escalate from "browser crash" into "run code in a place you really don't want attackers running code."
Also important: exploitation typically requires a user to visit a malicious webpage, which then triggers the vulnerability inside Chrome's renderer process.
CVE-2026-1862: Type confusion in V8
The bigger headline vulnerability is in V8, Chrome's JavaScript and WebAssembly engine.
Type confusion, in plain language, is when the engine gets tricked into treating data as the wrong "type" (for example, handling a value like it's a pointer when it isn't).
According to the advisory, attackers often use this style of bug to manipulate memory pointers, potentially enabling out-of-bounds memory access that can lead to arbitrary code execution inside the browser's sandboxed environment.
CVE-2026-1861: Heap buffer overflow in libvpx
The second issue sits in libvpx, the library used for VP8/VP9 video processing.
A heap buffer overflow happens when a process writes more data than a buffer can hold. In this case, the advisory notes an attacker could embed a malformed video stream on a webpage; when Chrome processes it, memory corruption can occur.
Most commonly that leads to a browser crash (DoS), but the advisory also notes it can sometimes be chained with other techniques to reach code execution.
Who is affected
The advisory lists the affected versions as:
What to do right now
Google has released patched stable versions, and the advisory recommends updating immediately:
To verify and update:
Final thoughts
This advisory is basically the classic "modern browser reality" story: a lot of power (JS, WASM, video codecs) means a lot of attack surface. The good news is there are stable fixes available, and the fastest way to reduce risk is simply to update and restart Chrome — especially if you're on those listed versions.




Comments