A serious security issue affecting cPanel and WebHost Manager is now being actively exploited, with hackers reportedly compromising thousands of websites that still rely on vulnerable versions of the software. For website owners, hosting providers, developers, and businesses that depend on shared or managed hosting, this is the kind of vulnerability that should be treated as urgent.
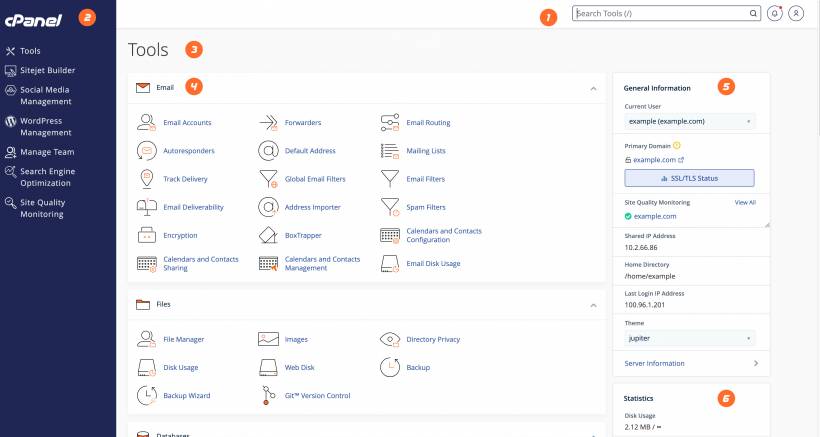
cPanel and WHM are widely used across the hosting industry. Many website owners may not even interact with WHM directly, but their hosting provider, reseller, or server administrator likely does. cPanel is commonly used to manage websites, email accounts, databases, DNS settings, backups, file managers, domains, SSL certificates, and other hosting features. Because it sits so close to the control layer of a website, a serious flaw in cPanel can quickly become a serious problem for every site hosted on that server.
Why This cPanel Vulnerability Is A Big Deal
The vulnerability, tracked as CVE-2026-41940, has been described as a critical flaw affecting cPanel and WHM. The concern is not only that the bug exists, but that attackers are already exploiting it in the wild.
According to reports, hackers have been using the flaw to take control of vulnerable servers through their control panels. That is especially dangerous because a hosting control panel is not just another web application. It is often the gateway to the entire hosting environment.
If an attacker gains access through cPanel or WHM, they may be able to manipulate website files, create or modify accounts, access databases, change configurations, upload malicious scripts, redirect visitors, steal data, or disrupt normal operations. In some cases, compromised sites may be defaced, used for phishing, injected with malware, or locked down as part of a ransomware-style attack.
Hundreds Of Thousands Of Servers May Still Be Exposed
Security monitoring organisation Shadowserver reportedly observed more than 550,000 potentially vulnerable servers running cPanel. That number had remained fairly stable for several days, suggesting that many systems had still not been updated quickly enough.
At the same time, the number of likely compromised cPanel instances was reported at around 2,000, down from an earlier figure of around 44,000. While that drop may sound reassuring, it does not mean the threat has disappeared. It could mean that some systems were cleaned up, patched, taken offline, or no longer showing clear signs of compromise. But the wider risk remains as long as vulnerable servers are still reachable online.
This is one of the difficult realities of internet-wide vulnerabilities. Once attackers know how to exploit a bug, they can scan the internet quickly and target as many exposed systems as possible. Website owners who delay updates may find themselves caught in the second or third wave of attacks, even if they were not targeted at the beginning.
Some Sites Showed Signs Of Ransomware Activity
Reports also suggest that some affected websites displayed messages from attackers claiming that the victim's files had been encrypted. Google had apparently indexed dozens of websites that, at some point, showed these ransom-style messages.
Some of those websites later returned to normal, but that does not necessarily mean the incident was harmless. A website may appear restored while still needing deeper investigation. Attackers may leave behind web shells, hidden administrator accounts, altered scripts, modified permissions, or malicious cron jobs. They may also have accessed data before the visible ransom note appeared.
This is why cleaning a compromised server is not simply about restoring the homepage. A proper response should include patching the vulnerable software, reviewing logs, rotating passwords, checking files for unauthorised changes, scanning for malware, validating backups, and confirming that no backdoor remains.
CISA Added The Bug To Its Known Exploited Vulnerabilities Catalog
The U.S. Cybersecurity and Infrastructure Security Agency added CVE-2026-41940 to its Known Exploited Vulnerabilities catalog after confirming that it was being exploited in the wild. That is an important signal because vulnerabilities are added to this catalog when there is evidence of active exploitation, not merely theoretical risk.
CISA also instructed U.S. federal agencies to patch quickly, with a deadline reportedly set for Sunday. While that requirement applies to U.S. government agencies, the message is relevant to everyone else too: this is not a vulnerability to leave for the next routine maintenance window.
For businesses, schools, small hosting companies, web agencies, and anyone running cPanel-managed servers, the practical lesson is simple. Patch now, then verify.
Attacks May Have Started Before Public Disclosure
One of the more concerning details is that attacks may have started much earlier than the public disclosure. KnownHost CEO Daniel Pearson reportedly said his company detected attacks as far back as 23 February.
If accurate, that means some attackers may have known about the flaw or were exploiting related behaviour before many administrators were aware of the risk. This also means server owners should not only patch going forward, but also review whether their systems may already have been accessed.
That part is easy to overlook. Many administrators assume that if they patched after the advisory, they are safe. But if exploitation happened before the patch, the server may already be compromised. Patching closes the door, but it does not remove an attacker who already got inside.
What Website Owners Should Do Now
For website owners who use shared hosting, the first step is to contact the hosting provider and ask whether their cPanel and WHM systems have been patched against CVE-2026-41940. Many shared hosting users do not control the server directly, so the responsibility falls on the provider.
For server administrators, the action should be more direct. Update cPanel and WHM immediately to the fixed version recommended by the vendor. After that, check whether the server shows signs of compromise. This should include reviewing access logs, cPanel logs, WHM activity, recently modified files, unknown users, suspicious PHP files, unusual redirects, and any unfamiliar scheduled tasks.
Administrators should also rotate passwords for affected accounts, especially root, reseller, cPanel users, database users, FTP accounts, email accounts, and any credentials stored inside configuration files. If there is any sign of compromise, assume credentials may have been exposed.
Backups should also be reviewed carefully. Do not blindly restore from a recent backup unless you are confident it was created before the compromise and is clean. Restoring a compromised backup can simply bring the attacker's files back into the environment.
Why Hosting Control Panels Are High-Value Targets
This incident is also a reminder of why hosting control panels are such attractive targets. A single vulnerable cPanel or WHM instance can represent access to many websites at once. For attackers, that is far more efficient than compromising one small website at a time.
A control panel also provides a convenient interface for managing files, databases, domains, email, and users. If an attacker gains control, they do not always need advanced techniques to cause damage. The panel itself may provide enough functionality to take over sites, create persistence, or disrupt services.
That is why administrators should protect cPanel and WHM with strong passwords, multi-factor authentication where available, IP restrictions where practical, regular updates, limited access, and proper monitoring. Security cannot depend only on patching after something goes wrong.
The Bigger Lesson For Businesses
For many businesses, the website is no longer just a brochure. It may handle customer enquiries, bookings, online payments, internal forms, support portals, downloads, e-commerce orders, or brand communications. If the hosting control panel is compromised, the impact can go beyond website downtime.
A hacked site can damage customer trust, affect search engine reputation, expose sensitive data, interrupt sales, and create cleanup costs. In regulated sectors, it may also trigger reporting obligations if personal data is involved.
This is why website security should be treated as part of business continuity. A company should know who manages its hosting, how updates are applied, how backups are protected, how quickly restoration can happen, and who responds if the site is compromised.
Final Thoughts
The mass exploitation of the cPanel and WHM vulnerability shows how quickly a critical hosting flaw can turn into a widespread security incident. With hundreds of thousands of potentially vulnerable servers reported and thousands of likely compromised instances identified, this is not a minor technical issue.
Website owners should not assume their hosting environment is safe simply because the website appears normal. If the server uses cPanel or WHM, the software must be patched, access should be reviewed, and signs of compromise should be investigated.
For hosting providers and administrators, the priority is clear: update immediately, check for intrusion, rotate credentials, validate backups, and harden access. A control panel is one of the most powerful parts of a hosting environment. If attackers gain control of it, they may gain control of everything behind it.





Comments